一週肝出Linux之遠端服務詳解(ssh遠端登入、scp遠端複製、sftp安全下載、TCP Wrappers存取控制)
目錄
一:理論
1:ssh概要
(1).SSH是傳輸層和應用層上的安全協定,它只能通過加密連線雙方對談的方式來保證連線的安全性。當使用ssh連線成功後,將建立使用者端和伺服器端之間的對談,該對談是被加密的,之後使用者端和伺服器端的通訊都將通過對談傳輸。
(2).SSH服務的守護行程為sshd,預設監聽在22埠上。
(3).所有ssh使用者端工具,包括ssh命令,scp,sftp,ssh-copy-id等命令都是藉助於ssh連線來完成任務的。也就是說它們都連線伺服器端的22埠,只不過連線上之後將待執行的相關命令轉換傳送到遠端主機上,由遠端主機執行。
(4).ssh使用者端命令(ssh、scp、sftp等)讀取兩個組態檔:全域性組態檔/etc/ssh/ssh_config和使用者組態檔~/.ssh/config。實際上命令列上也可以傳遞設定選項。它們生效的優先順序是:命令列設定選項 > ~/.ssh/config > /etc/ssh/ssh_config。
(5).ssh涉及到兩個驗證:主機驗證和使用者身份驗證。通過主機驗證,再通過該主機上的使用者驗證,就能唯一確定該使用者的身份。一個主機上可以有很多使用者,所以每臺主機的驗證只需一次,但主機上每個使用者都需要單獨進行使用者驗證。
(6).ssh支援多種身份驗證,最常用的是密碼驗證機制和公鑰認證機制,其中公鑰認證機制在某些場景實現雙機互信時幾乎是必須的。雖然常用上述兩種認證機制,但認證時的順序預設是gssapi-with-mic,hostbased,publickey,keyboard-interactive,password。注意其中的主機認證機制hostbased不是主機驗證,由於主機認證用的非常少(它所讀取的認證檔案為/etc/hosts.equiv或/etc/shosts.equiv),所以網路上比較少見到它的相關介紹。總的來說,通過在ssh組態檔(注意不是sshd組態檔)中使用指令PreferredAuthentications改變認證順序不失為一種驗證的效率提升方式。
(7).ssh使用者端其實有不少很強大的功能,如埠轉發(隧道模式)、代理認證、連線共用(連線複用)等。
(8).ssh伺服器端組態檔為/etc/ssh/sshd_config,注意和使用者端的全域性組態檔/etc/ssh/ssh_config區分開來。
(9).很重要卻幾乎被人忽略的一點,ssh登入時會請求分配一個偽終端。但有些身份認證程式如sudo可以禁止這種型別的終端分配,導致ssh連線失敗。例如使用ssh執行sudo命令時sudo就會驗證是否要分配終端給ssh。
2:ssh協定與埠號
SSH 主要由三部分組成:
- 傳輸層協定 [SSH-TRANS]
提供了伺服器認證,保密性及完整性。此外它有時還提供壓縮功能。 SSH-TRANS 通常執行在TCP/IP連線上,也可能用於其它可靠資料流上。 SSH-TRANS 提供了強力的加密技術、密碼主機認證及完整性保護。該協定中的認證基於主機,並且該協定不執行使用者認證。更高層的使用者認證協定可以設計為在此協定之上。
- 使用者認證協定 [SSH-USERAUTH]
用於向伺服器提供使用者端使用者鑑別功能。它執行在傳輸層協定 SSH-TRANS 上面。當SSH-USERAUTH 開始後,它從低層協定那裡接收對談識別符號(從第一次金鑰交換中的交換雜湊H )。對談識別符號唯一標識此對談並且適用於標記以證明私鑰的所有權。 SSH-USERAUTH 也需要知道低層協定是否提供保密性保護。
- 連線協定 [SSH-CONNECT]
將多個加密隧道分成邏輯通道。它執行在使用者認證協定上。它提供了互動式登入話路、遠端命令執行、轉發 TCP/IP 連線和轉發 X11 連線。
- 預設監聽伺服器的22號埠
啟動SSH伺服器後,sshd執行起來並在預設的22埠進行監聽(你可以用 # ps -waux | grep sshd 來檢視sshd是否已經被正確的執行了)如果不是通過inetd啟動的SSH,那麼SSH就將一直等待連線請求。當請求到來的時候SSH守護行程會產生一個子程序,該子程序進行這次的連線處理
實驗
二:實驗
實驗環境
ssh免密登入實驗
準備兩臺以上初始化完成的虛擬機器器,之前文章有詳細步驟
虛擬機器器1 ip:192.168.1.10 (客戶機)
虛擬機器器3 ip:192.168.1.30 (伺服器)
ssh使用者登入控制
通過命令ssh命令可以遠端登入sshd服務,為使用者提供一個安全的shell環境,以便對伺服器進行管理和維護。使用時應指定登入使用者、目標主機地址作為引數。
[root@server1 ~]# ssh root@192.168.1.30 #以root使用者登入伺服器
The authenticity of host '192.168.1.30 (192.168.1.30)' can't be established.
ECDSA key fingerprint is SHA256:mrvZ76+kad6pXTq4E+MReynzGrfGYSjgt3UezAg8yXk.
ECDSA key fingerprint is MD5:8d:4a:fe:2b:ca:19:2d:b3:b3:2b:6c:45:f6:26:0c:59.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.1.30' (ECDSA) to the list of known hosts.
root@192.168.1.30's password: #輸入密碼
Last failed login: Mon Sep 7 08:52:01 CST 2020 from 192.168.1.10 on ssh:notty
There were 2 failed login attempts since the last successful login.
Last login: Wed Sep 2 23:12:57 2020
[root@server3 ~]# exit #exit退出登入
登出
Connection to 192.168.1.30 closed.
1:不允許對方遠端root賬戶登入
[root@server3 ~]# vi /etc/ssh/sshd_config
37 #LoginGraceTime 2m #登入驗證時間為2分鐘
38 PermitRootLogin no #yes改為no 註釋去掉(禁止root登入)
39 #StrictModes yes
40 #MaxAuthTries 6 #最大重試次數為6次
41 #MaxSessions 10
42
43 #PubkeyAuthentication yes
[root@server3 ~]# systemctl restart sshd
[root@server3 ~]# useradd tom
[root@server3 ~]# echo "123123" | passwd --stdin tom
更改使用者 tom 的密碼 。
passwd:所有的身份驗證令牌已經成功更新。
[root@server1 ~]# ssh root@192.168.1.30
root@192.168.1.30's password:
Permission denied, please try again.
root@192.168.1.30's password:
Permission denied, please try again.
root@192.168.1.30's password:
Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).
[root@server1 ~]# ssh tom@192.168.1.30
tom@192.168.1.30's password:
[tom@server3 ~]$
[tom@server3 ~]$ su root
密碼:
[root@server3 tom]# cd
[root@server3 ~]#
#雖然靜止了tom1的禁止root賬戶登入還是不安全的 可以用主機的其他賬戶作為跳板登入2:禁止跳板登入
[root@server3 ~]# vi /etc/pam.d/su
#%PAM-1.0
auth sufficient pam_rootok.so
# Uncomment the following line to implicitly trust users in the "wheel" group.
#auth sufficient pam_wheel.so trust use_uid
# Uncomment the following line to require a user to be in the "wheel" group.
auth required pam_wheel.so use_uid #前面#註釋去掉
auth substack system-auth
auth include postlogin
account sufficient pam_succeed_if.so uid = 0 use_uid quiet
account include system-auth
password include system-auth
session include system-auth
session include postlogin
session optional pam_xauth.so
[root@server3 ~]# systemctl restart sshd
[root@server1 ~]# ssh tom@192.168.1.30
tom@192.168.1.30's password:
Last login: Mon Sep 7 09:44:44 2020 from 192.168.1.30
[tom@server3 ~]$ su root
密碼:
su: 拒絕許可權
[tom@server3 ~]$
測試最大密碼重試次數
#LoginGraceTime 2m
#PermitRootLogin yes
#StrictModes yes
MaxAuthTries 3 #開啟最大重試次數改為3次
#MaxSessions 10
[root@server1 ~]# ssh root@192.168.1.30
root@192.168.1.30's password:
Permission denied, please try again.
root@192.168.1.30's password:
Permission denied, please try again.
root@192.168.1.30's password:
Received disconnect from 192.168.1.30 port 22:2: Too many authentication failures
Authentication failed.
[root@server1 ~]# 設定黑白名單
[root@server3 ~]# vi /etc/ssh/sshd_config
AllowUsers tom@192.168.1.20
[root@server3 ~]# systemctl restart sshd
[root@server1 ~]# ssh tom@192.168.1.30
tom@192.168.1.30's password:
Permission denied, please try again.
tom@192.168.1.30's password:
Permission denied, please try again.
tom@192.168.1.30's password:
Received disconnect from 192.168.1.30 port 22:2: Too many authentication failures
Authentication failed.遠端配對金鑰驗證
1:檢視目錄.ssh資料夾下生成的公私鑰
[root@server1 ~]# ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): 123213
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in 123213.
Your public key has been saved in 123213.pub.
The key fingerprint is:
SHA256:BdJLDyAqC8kXp58BKOyQdrkIRzZNTCPatpxDB+gulKw root@server1
The key's randomart image is:
+---[RSA 2048]----+
|.+BB*.oo. |
|BO.BBo .+. |
|&oOoo. . +. |
|.&.=. o ... |
|= = o S |
|E. . |
|. |
| |
| |
+----[SHA256]-----+
[root@server1 ~]# cd ~/.ssh
[root@server1 .ssh]# ls
id_rsa id_rsa.pub known_hosts #id_rsa (私鑰) id_rsa.pub (公鑰)2:上傳公鑰到伺服器
[root@server1 .ssh]# ssh-copy-id root@192.168.1.30伺服器檢視
[root@server3 ~]# cd ~/.ssh/
[root@server3 .ssh]# vi authorized_keys 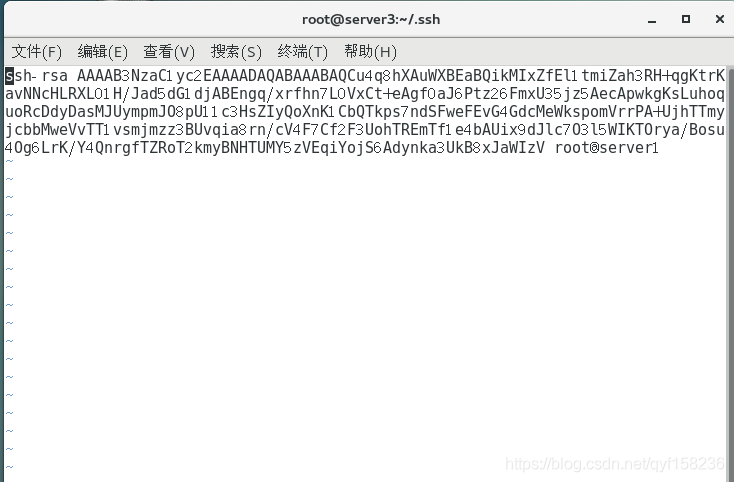
3:測試登入
[root@server1 .ssh]# ssh 192.168.1.30scp遠端安全複製
通過scp命令可以利用SSH安全連線與遠端主機相互複製。使用scp命令時,除了必須指令複製源、目標之外,還應指定目標主機地址、登入使用者、執行後提示驗證口令即可
[root@server1 opt]# scp test.txt root@192.168.1.30:/root
The authenticity of host '192.168.1.30 (192.168.1.30)' can't be established.
ECDSA key fingerprint is SHA256:mrvZ76+kad6pXTq4E+MReynzGrfGYSjgt3UezAg8yXk.
ECDSA key fingerprint is MD5:8d:4a:fe:2b:ca:19:2d:b3:b3:2b:6c:45:f6:26:0c:59.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.1.30' (ECDSA) to the list of known hosts.
root@192.168.1.30's password:
test.txt 100% 4 1.9KB/s 00:00
[root@server3 ~]# ls -lh
總用量 12K
-rw-------. 1 root root 1.9K 8月 26 17:58 anaconda-ks.cfg
-rw-r--r--. 1 root root 2.0K 8月 26 18:30 initial-setup-ks.cfg
-rw-r--r--. 1 root root 4 9月 7 09:24 test.txt
drwxr-xr-x. 2 root root 6 8月 26 18:31 公共
drwxr-xr-x. 2 root root 6 8月 26 18:31 模板
drwxr-xr-x. 2 root root 6 8月 26 18:31 視訊
drwxr-xr-x. 2 root root 6 8月 26 18:31 圖片
drwxr-xr-x. 2 root root 6 8月 26 18:31 檔案
drwxr-xr-x. 2 root root 6 8月 26 18:31 下載
drwxr-xr-x. 2 root root 6 8月 26 18:31 音樂
drwxr-xr-x. 2 root root 6 8月 26 18:31 桌面
#已經複製成功
[root@server1 opt]# scp -r tom/ root@192.168.1.30:/opt
root@192.168.1.30's password:
a.txt 100% 5 1.3KB/s 00:00
b.txt 100% 5 3.6KB/s 00:00
#-r 表示遞迴目錄sftp安全FTP 上下載
通過sftp命令可以利用SSH安全連線與遠端主機上傳,下載檔案,採用了與FTP類似的登入過程和互動環境,便於目錄資源管理
[root@server1 ~]# sftp 192.168.1.30
The authenticity of host '192.168.1.30 (192.168.1.30)' can't be established.
ECDSA key fingerprint is SHA256:mrvZ76+kad6pXTq4E+MReynzGrfGYSjgt3UezAg8yXk.
ECDSA key fingerprint is MD5:8d:4a:fe:2b:ca:19:2d:b3:b3:2b:6c:45:f6:26:0c:59.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.1.30' (ECDSA) to the list of known hosts.
root@192.168.1.30's password:
Connected to 192.168.1.30.
sftp> ls
anaconda-ks.cfg b.txt initial-setup-ks.cfg
下載 公共 圖片
檔案 桌面 模板
視訊 音樂
sftp> get b.txt
Fetching /root/b.txt to b.txt
/root/b.txt 100% 7 3.9KB/s 00:00
sftp> put a
a.txt anaconda-ks.cfg
sftp> put a.txt
Uploading a.txt to /root/a.txt
a.txt 100% 7 10.4KB/s 00:00
sftp> byeTCP Wrappers存取概述
TCP_Wrappers有一個TCP的守護行程叫作tcpd。以ssh為例,每當有ssh的連線請求時,tcpd即會截獲請求,先讀取系統管理員所設定的存取控制檔案,符合要求,則會把這次連線原封不動的轉給真正的ssh程序,由ssh完成後續工作;如果這次連線發起的ip不符合存取控制檔案中的設定,則會中斷連線請求,拒絕提供ssh服務
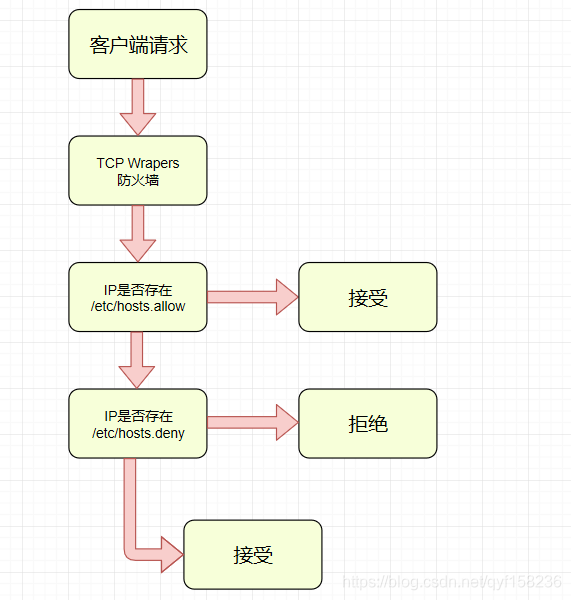
存取控制策略的組態檔:
-
etc/hosts.allow
-
etc/hosts.deny
範例:
在伺服器修改組態檔hosts.allow,允許的IP地址為192.168.1.10存取,其他的都是不可以存取的
[root@server3 ~]# vi /etc/hosts.allow
#
# hosts.allow This file contains access rules which are used to
# allow or deny connections to network services that
# either use the tcp_wrappers library or that have been
# started through a tcp_wrappers-enabled xinetd.
#
# See 'man 5 hosts_options' and 'man 5 hosts_access'
# for information on rule syntax.
# See 'man tcpd' for information on tcp_wrappers
#
sshd:192.168.1.10 #允許IP為192.168.1.10可以通過ssh遠端存取#
# hosts.deny This file contains access rules which are used to
# deny connections to network services that either use
# the tcp_wrappers library or that have been
# started through a tcp_wrappers-enabled xinetd.
#
# The rules in this file can also be set up in
# /etc/hosts.allow with a 'deny' option instead.
#
# See 'man 5 hosts_options' and 'man 5 hosts_access'
# for information on rule syntax.
# See 'man tcpd' for information on tcp_wrappers
#
sshd:ALL #拒絕其他存取測試1
#地址為192.168.1.10的客戶機
[root@server1 ~]# ssh root@192.168.1.30
root@192.168.1.30's password:
Last login: Mon Sep 7 08:52:41 2020 from 192.168.1.10
[root@server3 ~]#
#地址為192.168.1.20的客戶機
[root@server2 ~]# ssh 192.168.1.30
ssh_exchange_identification: read: Connection reset by peer測試2
# hosts.allow This file contains access rules which are used to
# allow or deny connections to network services that
# either use the tcp_wrappers library or that have been
# started through a tcp_wrappers-enabled xinetd.
#
# See 'man 5 hosts_options' and 'man 5 hosts_access'
# for information on rule syntax.
# See 'man tcpd' for information on tcp_wrappers
#
sshd:192.168.1.10
將hosts.allow檔案和hosts.deny都同時設定同一個IP地址
[root@server1 ~]# ssh root@192.168.1.30
root@192.168.1.30's password:
Last login: Mon Sep 7 10:58:05 2020 from 192.168.1.20
#可以存取測試3
地址也可以寫目標網段
# hosts.deny This file contains access rules which are used to
# deny connections to network services that either use
# the tcp_wrappers library or that have been
# started through a tcp_wrappers-enabled xinetd.
#
# The rules in this file can also be set up in
# /etc/hosts.allow with a 'deny' option instead.
#
# See 'man 5 hosts_options' and 'man 5 hosts_access'
# for information on rule syntax.
# See 'man tcpd' for information on tcp_wrappers
#
sshd:192.168.1.*
[root@server1 ~]# ssh root@192.168.1.30
ssh_exchange_identification: read: Connection reset by peer
[root@server1 ~]#
#客戶機存取失敗 如果您覺得對您有用的話,三連吧,求求啦!!